Secure Architecture for SaaS: The Founder's Guide
How founders and CTOs build a GDPR-aligned, scalable, security-by-design architecture that holds up under real growth pressure — without retrofits.

If you build a B2B SaaS product and treat security as a downstream task, you almost always pay the price at the worst possible moment. The familiar pattern: the first growth phase after launch quietly exposes data-access gaps because the architecture was originally designed for ten users, not ten thousand. Security can't be bolted on like an upgrade. This guide walks through how founders and CTOs systematically build a GDPR-aligned, scalable, security-by-design architecture from day one — one that holds up under real growth pressure.
Table of Contents
- Foundations of Secure Architecture for B2B SaaS
- Preparation: Tools, Methods, Requirements
- Step by Step: Implementing a Secure Architecture
- Verification: Continuously Auditing Security
- Field Notes: Why Security-by-Design Makes the Difference
- Mastering Secure Architecture with Experts
- Frequently Asked Questions on Secure Architecture
Key Takeaways
| Point | Detail |
|---|---|
| Implement Security-by-Design | Plan security early and systematically against established principles and checklists. |
| GDPR as architectural foundation | Every technical decision should reflect — and document — GDPR requirements. |
| Choose tools and methods deliberately | Use vetted automation and checklist tools to build a robust security architecture. |
| Continuous security verification | Integrated tests and ongoing checks sustain compliance and protection. |
| Expert help for complex cases | Where uncertainty is real, professional advice is the cheapest investment in your product and your customers. |
Foundations of Secure Architecture for B2B SaaS
Secure software architecture doesn't start with tools or checklists. It starts with a design decision: treating security as a structural property of the system, not as a protective layer added later.
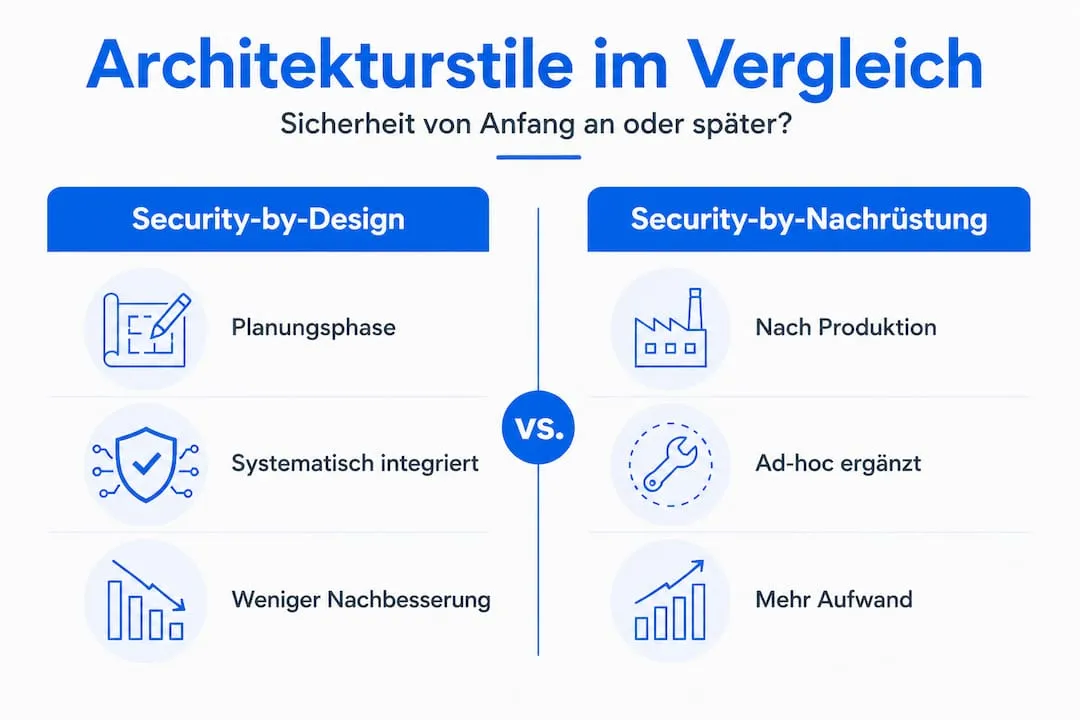
Security-by-Design vs. Security-by-Default
The two concepts are often conflated, but they describe different things. Security-by-Design means that security principles are actively considered throughout planning and development. Every architectural decision is paired with one question: how can this subsystem be attacked, and how do we eliminate the attack surface up front?
Security-by-Default describes the state of a shipped system. Default configurations are safe. Open ports, broad permissions and missing encryption don't exist in the initial state. Together, the two produce an architecture that systematically applies 22 security principles across the entire product lifecycle, as the ENISA Security-by-Design-and-Default playbook describes.
| Trait | Security-by-Design | Security as Retrofit |
|---|---|---|
| Timing | Planning phase | After production release |
| Cost | Low (preventive) | High (reactive) |
| Effectiveness | Structural | Locally limited |
| GDPR conformance | Provably integrated | Hard to document |
| Scalability | Considered from day one | Forces a rewrite |
Core architectural principles
Three principles form the foundation of a secure system architecture for B2B SaaS:
- Separation of concerns: Each component has exactly one defined function. Authentication logic doesn't live inside business logic. Data access is isolated from presentation layers.
- Modularity: The system is composed of decoupled building blocks that can be updated, audited and replaced independently. A security incident in one module doesn't automatically spread to others.
- Least privilege: Each service, user and process gets only the permissions strictly required for its function. No broad admin roles by default.
GDPR mandates technical and organisational measures (TOMs) that map directly onto these principles. Data minimisation, purpose limitation and access logging aren't optional features; they're legal requirements that must be reflected in the architecture. Building a scalable software architecture GDPR-aligned from day one saves substantial work in later audits.
"A secure architecture isn't a security product. It's a design property of the entire system, visible in every layer."
Other engineering perspectives on the topic show how leading teams operationalise these principles — and which architectural calls most often decide between long-term success and accumulating technical debt.
Preparation: Tools, Methods, Requirements
Before a line of code is written, the architecture should sit on a documented foundation. The preparation phase decides whether the resulting system is provably secure, or merely intuitively built.
Overview of architecture tools and methods
Choosing the right tools is a strategic decision, not a pure technical one. The following categories cover the entire security lifecycle:
- Threat modelling: STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) is a proven framework for systematically identifying attack vectors. OWASP Threat Dragon supports visual modelling.
- Static code analysis (SAST): Tools like SonarQube or Checkmarx scan source code for known security patterns before the system runs.
- Dependency scanning: Snyk or OWASP Dependency-Check identify vulnerable libraries in the dependency chain — a risk often overlooked in startups.
- Infrastructure-as-Code review: Terraform configurations and Kubernetes manifests are checked with Checkov or Trivy for unsafe defaults.
- Penetration testing: Automated baseline scans with OWASP ZAP, complemented by manual penetration testing before critical releases.
| Tool category | Examples | When it's used |
|---|---|---|
| Threat modelling | STRIDE, OWASP Threat Dragon | Design phase |
| Static analysis (SAST) | SonarQube, Checkmarx | Development phase |
| Dependency scanning | Snyk, OWASP Dependency-Check | CI/CD integration |
| IaC security | Checkov, Trivy | Infrastructure planning |
| Dynamic tests (DAST) | OWASP ZAP, Burp Suite | Pre-release |
Define requirements clearly
Defining requirements before implementation isn't a bureaucratic act. It's the foundation for every security decision that follows. Three dimensions need to be captured fully:
Scalability: What load profiles are expected? A B2B SaaS product with a hundred customers at launch can be serving ten thousand within twelve months. Security mechanisms — rate limiting, session management, database access controls — must be sized for that growth from day one.
GDPR requirements: Which data categories are processed? Where is data stored? Hosting in Germany or the EU is an architectural decision, not a later add-on. Data-processing agreements, deletion routines and access processes must be technically represented.
Security goals: What are the system's protected assets? Customer data, payment information, contracts? Each asset gets a defined protection level that drives architectural decisions. Practical implementation patterns help translate these requirements into concrete architecture.
The ENISA playbook confirms that checklists and evidence requirements are particularly practical for SMEs, because they structure documentation effort without producing unnecessary complexity. The H-Studio knowledge library contains complementary resources for structured requirements analysis.
Pro tip: Tool selection should be aligned early with all relevant stakeholders. The most important deliverable is documenting the interfaces between security tools and the CI/CD pipeline. Gaps in interface documentation become audit gaps later.
Step by Step: Implementing a Secure Architecture
Implementing a secure architecture follows a clear sequence. Each step builds on the previous one and produces documentable security properties.
1. Foundation: Separation of Concerns in practice
The first implementation step is the structural separation of system components. In a typical Java/Spring Boot architecture, that means separate services for authentication, authorisation, business logic and data access. No service class takes on more than one of these roles.
In practice this is implemented as a layered architecture or via the ports-and-adapters pattern (hexagonal architecture). The latter has the advantage that security tests for each adapter can be written in isolation, without touching the core logic. For microservices-based systems, an API gateway is added as the central entry point — handling authentication and rate limiting before any downstream service.
2. Default Hardening: standardised protection
Every system starts in a maximally restrictive state. Concrete measures:
- HTTPS as the only allowed transport protocol; HTTP requests redirect automatically.
- Database connections only over encrypted channels with certificate validation.
- No direct database access from the public network — only via dedicated service layers.
- Default passwords for every system component must be replaced on first start.
- Security headers (Content Security Policy, HSTS, X-Frame-Options) by default in every HTTP response.
3. Operational Integrity: automated security tests
Security isn't a one-time state. It must be verified at every deployment. ENISA's playbooks give concrete instructions for translating security-by-design into automated processes.
In the CI/CD pipeline:
- Pre-commit hooks: Block secrets like API keys or passwords from being committed, using tools such as git-secrets or detect-secrets.
- Build phase: SAST scanners analyse code on every commit. Critical findings block the build.
- Test phase: Security-relevant unit and integration tests check access control, input validation and error behaviour.
- Deployment phase: IaC scans check infrastructure configurations before delivery. Unsafe Terraform modules are rejected.
4. Guided Protection: usable security for end users
A frequently neglected aspect is security guidance for end users. Bad UX around security functions produces unsafe user behaviour. Concretely:
- Clear password requirements with real-time feedback — no cryptic error messages after submission.
- Multi-factor authentication (MFA) as the recommended default, not a hidden option.
- Session management with transparent timeouts and clear communication about active sessions.
- Privacy settings that are accessible and understandable for users.
Pro tip: A common mistake is planning MFA only as a post-launch feature request. Integration costs for MFA rise sharply once the identity system is already in production. OAuth2/OIDC flows with MFA support should be planned from sprint one.
Statistic: Systems that adopt security-by-design from the start reduce the cost of incidents and post-hoc fixes by an average factor of six versus systems that retrofit security later, according to multiple industry studies.
Concrete implementation examples across different industries and product domains show how these steps vary depending on the regulatory context. The blog on web engineering holds complementary technical write-ups for the implementation phase.
Verification: Continuously Auditing Security
After implementation, ongoing operations begin. Security isn't a static state a system permanently holds after a successful deployment. It has to be actively maintained, audited and documented.
Verification methods and release gates
A release gate is a defined checkpoint a release must pass before reaching production. Without evidence — provable security-check results — no release is approved. The ENISA playbook is explicit: evidence and checks as a release gate are mandatory for secure software.
These verification methods belong in every process:
- Automated SAST and DAST scans on every release candidate, with documented results and defined thresholds for acceptable findings.
- Penetration tests at least annually and before major releases, conducted by independent security professionals.
- Dependency audits after every third-party library update, so newly disclosed CVEs are caught immediately.
- Configuration reviews for cloud infrastructure and Kubernetes clusters against CIS benchmarks.
- Data Protection Impact Assessments (DPIAs) for new data processing activities, systematically anchored in the architecture.
Collecting and documenting evidence
Documentation isn't bureaucracy. It's the operational memory of the system and the foundation for audits, investor conversations and customer certifications. Relevant evidence types:
- Scan reports: Exported SAST/DAST results with timestamps and version references.
- Penetration test reports: Findings with risk classifications and remediation evidence.
- Change logs for security measures: When was which configuration changed, and why?
- Access log excerpts: For GDPR-relevant systems, regularly archived.
"Security documentation that can't be found when it matters has no value. Automated evidence collection isn't a comfort feature; it's an operational necessity."
Common verification mistakes to avoid
Three patterns appear especially often in practice:
- Audit only on suspicion: Security checks aren't run routinely, only after an incident. That eliminates the preventive effect.
- No clear ownership: It's unclear who in the team is responsible for executing and documenting security checks. Distributed responsibility is, in practice, no responsibility.
- Test coverage without business context: Automated tests check technical parameters but not whether access controls actually reflect the business rules. A user with the role "Guest" must not be able to invoke admin functions, even when the system is technically configured correctly.
Real startup project examples illustrate where these gaps emerge in practice and how they get closed structurally. Teams running complex data flows will also find security perspectives for data-centric components in our analytics pipeline approach.
Pro tip: Compliance checks in CI/CD should include both blocking and informational rules. Blocking rules prevent deployment on critical findings. Informational rules notify the security team about medium risks without halting development. The split avoids both security gaps and the productivity loss of overly restrictive automation.
Field Notes: Why Security-by-Design Makes the Difference
There's an uncomfortable truth that rarely surfaces in security consulting: most startups that have a security problem after twelve to eighteen months had it from day one. It just wasn't visible yet.
Security problems scale with the system. A missing access validation in an endpoint that was never tested at one hundred users becomes the entry point at ten thousand. A flawed permission model that didn't bother anyone at MVP launch suddenly blocks ISO-27001 certification during enterprise sales.
The actual difference between teams that successfully apply security-by-design and those that don't isn't technical knowledge. It's design discipline. The question "How can this go wrong?" gets asked at every architectural decision — not afterwards.
Another underestimated factor is security culture inside the team. Establishing security as collective responsibility is harder than implementing any single technical control. Teams that treat security as a quality property — not as the security officer's job — produce demonstrably more robust systems. That shows up especially in code review: when reviews systematically include security aspects, problems are caught before they reach production.
Preventive design takes time. Retrofitting takes considerably more — and not just in developer hours. A security incident during a growth phase consumes management capacity, damages customer trust, and can derail a fundraising round entirely. The ROI on security-by-design is unambiguous in that calculation. Founder teams that understand this early build systems that don't only launch securely, but scale securely too. That's the core of scalable software architecture as a strategic advantage.
Mastering Secure Architecture with Experts
Building a secure, GDPR-aligned architecture alone is unrealistic for most founder teams. It requires not just technical know-how, but experience with the specific failure modes of regulated industries and scalable systems.
H-Studio works with funded B2B SaaS startups to set this foundation correctly from day one. From an Architecture Sprint (5 days, €3,500) before MVP launch through long-term Engineering Partnership as an external senior team, we walk teams through every step of this guide. Our engineering services cover architecture reviews, GDPR-aligned implementation and DevOps integration. Teams planning enterprise-grade engineering from the start avoid the costly rewrite trap and create the conditions for Series-A-ready system quality. Talk to us before the first line of code is written.
Frequently Asked Questions on Secure Architecture
What does Security-by-Design concretely mean for SaaS startups?
Security-by-Design guarantees that security principles and checks are integrated into the system from the start, instead of being patched in later. The ENISA playbook describes 22 principles for embedding security across the entire product lifecycle.
How does GDPR shape architectural decisions?
GDPR defines data-protection requirements that must be implemented and proven through technical and organisational measures. Checklists and evidence requirements from ENISA's playbooks help SMEs meet those requirements in a structured way.
Which tools are recommended for security architecture?
Playbooks and structured checklists like ENISA's help with planning and verification; automated tools like SonarQube, Snyk and Checkov complement the technical implementation. ENISA's playbooks give concrete instructions for tool integration into the development process.
How do you integrate security checks efficiently into daily development?
Automated tests and CI/CD checks provide continuous control and documentation in the development process. ENISA requires evidence as a release gate — meaning no deployment without provable security checks.
Read more
Join our newsletter!
Enter your email to receive our latest newsletter.
Don't worry, we don't spam
Popular Articles

Evolutionary Architectures: Ho
Anna Hartung

Scalable Backend Systems: Arch
Anna Hartung

Building Production-Ready SaaS
Anna Hartung
Continue Reading
SaaS in B2B: Architecture, Scaling and Compliance
Discover what SaaS really means for B2B startups: architecture, scaling and compliance. Avoid the common mistakes and secure your growth.
Building Production-Ready SaaS: Scalable and GDPR-Compliant
How to build production-ready SaaS systems: scalable multi-tenant architecture, GDPR compliance, and an engineering standard for the DACH market.
How to Build Software That Survives German Compliance
Not 'passes GDPR'—but survives audits, legal reviews, and real enterprise pressure. In Germany, compliance is not an event. It's an operating condition. Software that doesn't internalize this will eventually stall—in sales, scaling, or trust.
Scalable Backend Systems: Architecture for SaaS Growth
Which backend architectures hold up as a B2B SaaS grows? Multi-tenant models, resilience patterns and microservice granularity for 12 to 24 months of real growth.
Evolutionary Architectures: How B2B SaaS Scales Without a Rewrite
How B2B SaaS teams design software so it grows with the business — without the painful 18-month rewrite. Modulith-First, Strangler-Fig, fitness functions.
Local AI vs Cloud AI: GDPR Reality for German Companies
What actually works—and what breaks deals. In Germany, AI discussions end with GDPR, data protection officers, and one question: 'Where does the data go?' Learn when cloud AI works, when it doesn't, and why local AI is becoming a competitive advantage.
See how we implement this in practice
Explore our case studies demonstrating these technologies and approaches in real projects

EventStripe
Event Management & Payment Processing Platform - Scalable event ticketing and payment processing system.
Learn more →
VTB Bank
Real-Time Data Streaming Platform - High-performance data-streaming platform capable of processing millions of financial messages per second.
Learn more →
PlayDeck - Powering Telegram's Gaming Ecosystem
How we built the backend architecture for Telegram's fastest-growing gaming platform.
Learn more →